💦Titanic's Fate | A Stark Reminder for Cybersecurity ⚓
Learn from the Titanic: Strengthen Your Cybersecurity Beyond Firewalls

Driving SD-WAN Adoption in South Africa
When we think of the Titanic, we often recall the colossal iceberg it struck on that fateful night. Yet, if we look beyond the surface, we uncover a profound lesson that echoes loudly in the world of cybersecurity. The Titanic's demise was not solely due to the iceberg's impact; it was a culmination of structural weaknesses, much like those found in modern cybersecurity practices.
The Titanic's Tragedy | A Lesson in Causation
At first glance, the Titanic's collision with the iceberg is the immediate cause of its sinking. However, delve a bit deeper, and you find the intermediate causation – the iceberg tearing a hole below the waterline. Yet, the true root causation lay in the ship's flawed construction. Its watertight compartments, intended to prevent disaster, were only partially effective. When one filled with water, it spilled into adjacent compartments, sealing the Titanic's fate.
The Cybersecurity Parallels
In the world of cybersecurity, we find ourselves at a similar crossroads. We have implemented concepts like Zones and segmentation, akin to the Titanic's bulkheads, but their application often falls short. Many organizations lack comprehensive Zones or fail to ensure that their cybersecurity defenses are "full height."
Mitigating Threats through Zones & Segmentation
Imagine Zones as the modern cybersecurity equivalent of watertight compartments. Just as with the Titanic, the compromise of one should not endanger the integrity of others. Two significant threat vectors, Windows RDP and Network VPNs, can be likened to the Titanic's compromised compartments, granting hackers lateral movement within an organization.
Best Practices for Cybersecurity
VPN Placement: VPNs should never terminate on a firewall bridging zones; they should reside in a DMZ, isolated from critical systems.
Segmentation Strategies: When an application's RDP access is compromised, it should not open the floodgates to sensitive data. Segmentation strategies must isolate machines and services effectively.
Firewalls and the Swiss Victorinox Analogy: Don't believe in the myth that your firewall can do it all. A firewall should not serve as a Swiss Victorinox pocket knife. It's not a panacea for all cybersecurity challenges. Effective zoning, segmentation, and threat detection require a more comprehensive approach.
Wrap
The Titanic's tragic tale serves as a stark reminder for the world of cybersecurity. To avoid similar disasters, we must build stronger digital fortresses, where Zones and segmentation are as impenetrable as watertight compartments. Let us not fall for the allure of one-size-fits-all solutions; instead, let's craft a cybersecurity strategy as resilient as the Titanic should have been.
In this ever-evolving landscape, remember that not all guidance is equal. Just as the Titanic's builders couldn't rely solely on superficial solutions, we must not blindly trust every piece of advice, especially the snake oil sometimes presented to us by industry sources. Gartner, while valuable, should not be the sole compass guiding our cybersecurity journey.
As we navigate the turbulent waters of the digital age, let the lessons of the Titanic guide us toward a more secure future, guided by a discerning eye and a commitment to robust cybersecurity practices.
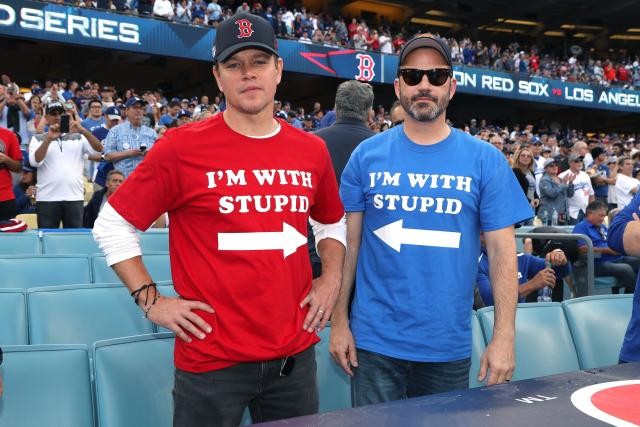
Don't be these guys...
Ronald Bartels ensures that Internet inhabiting things are connected reliably online at Fusion Broadband South Africa - the leading specialized SD-WAN provider in South Africa. 👉 Learn more about the best SD-WAN in the world: Contact Fusion🚀




