Revolutionizing Wide Area Networking
What is SD-WAN (Software Defined Wide Area Networking)? | The Mechanics of this Groundbreaking New Network Technology

Driving SD-WAN Adoption in South Africa
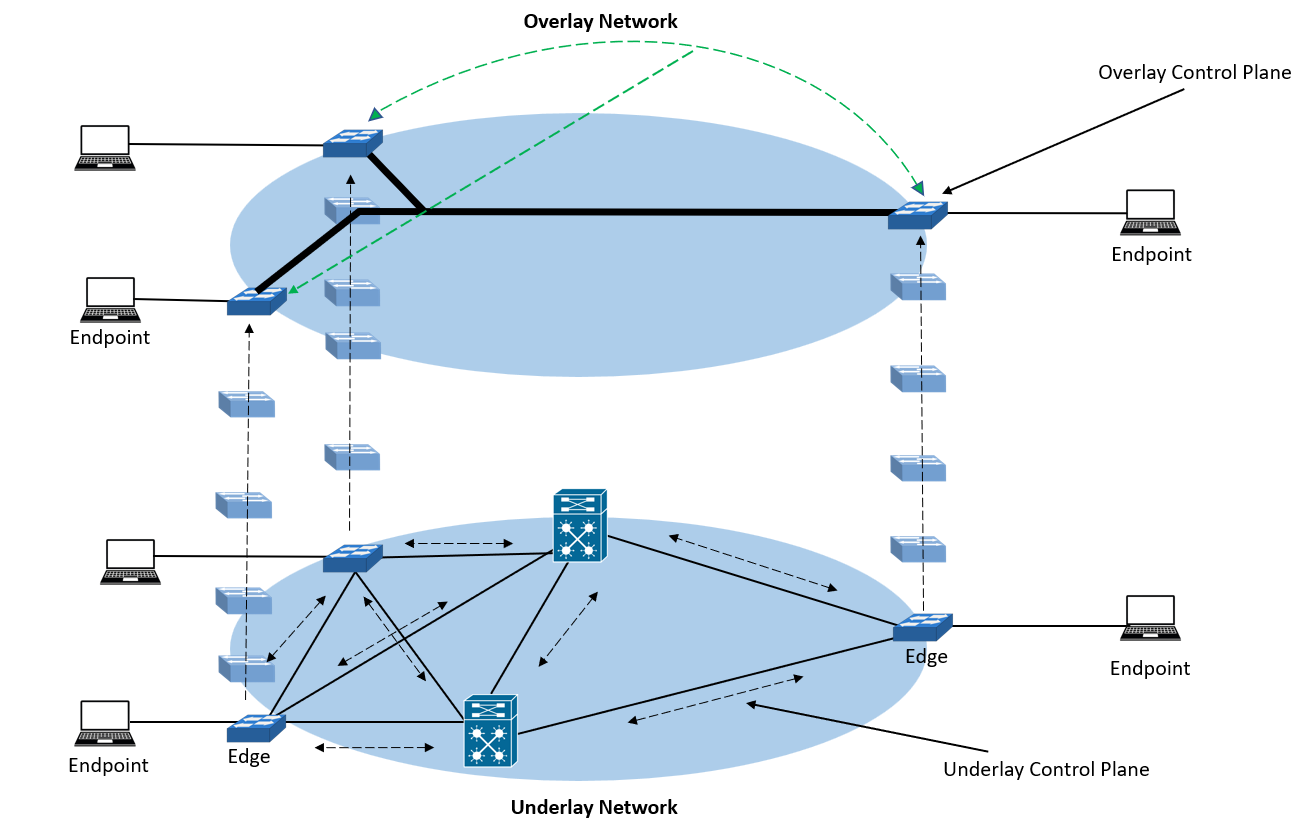
Software-Defined Wide Area Networking (SD-WAN) represents a paradigm shift in how businesses manage and optimize their network connectivity. At its core, SD-WAN is a software overlay that sits atop a traditional telecommunications underlay, abstracting the complexities of physical infrastructure to deliver intelligent, agile, and secure networking. This overlay not only enhances performance but also introduces features like WAN optimization, compression, bandwidth adaption, flapping, MTU correction, and accelerates application delivery across distributed environments.
Underlay vs Overlay Routing | NetworkAcademy.IO
Unlike simplistic views propagated by some vendors—who have merely rebranded their site-to-site Virtual Private Networks (VPNs) as SD-WAN to focus solely on branch networking—true SD-WAN encompasses a broader scope, including cloud integration, isolated sites, and advanced security postures.
Separating Planes | Management & Data
One of the foundational mechanics of SD-WAN is its separation into distinct planes: the management plane and the data plane. These are independent functions, ensuring that control and forwarding operations do not interfere with each other. The management plane, often referred to as the control plane in broader SDN contexts, handles orchestration, policy enforcement, and monitoring. It is encrypted end-to-end and designed never to be exposed to the public Internet, mitigating risks of unauthorized access. This design principle is crucial; exposing the management plane can lead to severe vulnerabilities, as seen in cases like Fortinet's infrastructure, which has faced multiple exploits due to flaws in VPN and management interfaces, making it one of the most targeted systems globally. In contrast, the data plane focuses on packet forwarding, routing traffic efficiently based on instructions from the management plane.
This separation allows for centralized control while distributing data handling, improving scalability and resilience. For instance, protocols manage route distribution and policy application across the overlay.
What is SD-WAN? | NetworkAcademy.IO
Zero Trust Control in SD-WAN Networks
SD-WAN operates on a zero trust model, where end nodes—such as branch routers, cloud edges, or remote devices—are strictly controlled. By default, nodes only communicate with the management servers, which authenticate and authorize interactions. These servers provide dynamic instructions on permissible communications, specifying paths and services without relying on static firewall rules that are prone to human error or oversight.
In a zero trust architecture, every access request is verified, regardless of location, using continuous authentication and micro-segmentation. This prevents lateral movement by threats and ensures that only authorized traffic traverses the data plane. Automation is prerequisite here; policies are pushed automatically, adapting in real-time to threats or changes. This mechanic elevates SD-WAN beyond legacy systems, where clumsy, manual configurations often lead to misconfigurations and security gaps.
Intelligent Handling of Underlay States
The management plane maintains comprehensive awareness of the underlay's state, monitoring metrics like packet loss, latency, jitter, and bandwidth utilization. This information is relayed back to central servers, enabling proactive path adjustments. Unlike traditional routers that might blackhole entire paths during issues, SD-WAN can restrict only the affected uplink or downlink segments, maintaining optimal performance.
For example, if an MPLS link experiences high latency, SD-WAN can reroute traffic to a broadband or fixed wireless alternative seamlessly, using techniques like forward error correction or per-packet steering. This granular control represents a significant leap from legacy protocols, ensuring business continuity and enhanced user experience.
Extending Beyond Branches | Isolated Sites & Cloud Integration
While often associated with branch connectivity, SD-WAN excels in supporting isolated sites that leverage cloud servers or data center-based services for Internet access and cybersecurity. These sites might include remote workers, IoT deployments, or pop-up locations, all benefiting from the overlay's flexibility.
SD-WAN abstracts the underlay—whether MPLS, broadband, 5G, or satellite—allowing seamless integration with cloud providers like AWS or Azure. This enables direct internet breakouts, reducing backhaul costs and latency, while maintaining security through encrypted overlays.
Modern Overlays | Moving Past IPSEC
Traditional IPSEC tunnels, while secure, are considered outdated for modern SD-WAN, as critiqued by figures like Linus Torvalds for their rigidity. Contemporary implementations favor proprietary or advanced overlays that optimize encryption, key exchanges, and performance. For instance, SD-WAN often streamlines IPSEC by eliminating unnecessary phases, incorporating non-layer 3 security for better efficiency, or using alternatives like WireGuard for faster, lighter tunnels.
This evolution supports dynamic path selection and application-aware routing, far surpassing dinosaur-era IPSEC in scalability and speed.
Network Layer - Study CCNP
Cloud-Based Portals | Visibility & Diagnostics
Fundamentally, SD-WAN shifts management from command-line interfaces (CLI) to intuitive, cloud-based portals. These portals offer multi-tenanted and hierarchical visibility, allowing administrators to monitor telecommunications, performance metrics, and traffic analytics across the network.
With built-in diagnostics, operators can troubleshoot issues in real-time, correlating underlay health with overlay performance. This moves toward the ideal of a "single pane of glass," where all network insights are centralized, simplifying operations for enterprises with global footprints.
Service Chaining & Agnostic Integration
SD-WAN thrives in service-chained environments, remaining agnostic to the underlay and integrated cybersecurity services. It supports upstream and downstream firewall integration from any vendor, ensuring compatibility in heterogeneous setups.
Through Network Function Virtualization (NFV), firewalls and edge services can be deployed virtually on-premises, managed securely via the overlay. This allows chaining of functions—like intrusion detection, content filtering, and load balancing—without hardware dependencies, enhancing flexibility and reducing costs.
The Essence of Automation
Automation is not an add-on but the core of SD-WAN mechanics. Edge nodes deploy via zero-touch provisioning (ZTP), where devices auto-register, pull configurations, and integrate without manual input. All interactions between management servers, orchestrators, and nodes are automated, eschewing cumbersome UIs with hundreds of settings.
Many purported SD-WAN "features" are merely workarounds for flawed architectures—true SD-WAN embeds automation deeply, ensuring rapid scaling and minimal operational overhead.
Wrapping up, SD-WAN's mechanics transcend basic connectivity, offering a sophisticated, secure, and automated framework that adapts to modern digital demands. By leveraging overlays, zero trust principles, and intelligent automation, it paves the way for resilient, efficient networks in an increasingly distributed world.

Ronald Bartels | LinkedIn | Instagram



