👀The Invisible Threat | Overlooking Insecure Protocols in Business Networks 🖨️
🚫🔍 Illuminate your network vulnerabilities with Fusion Broadband South Africa's tool, shedding light on the plaintext transmission of sensitive data✨🔒
Driving SD-WAN Adoption in South Africa
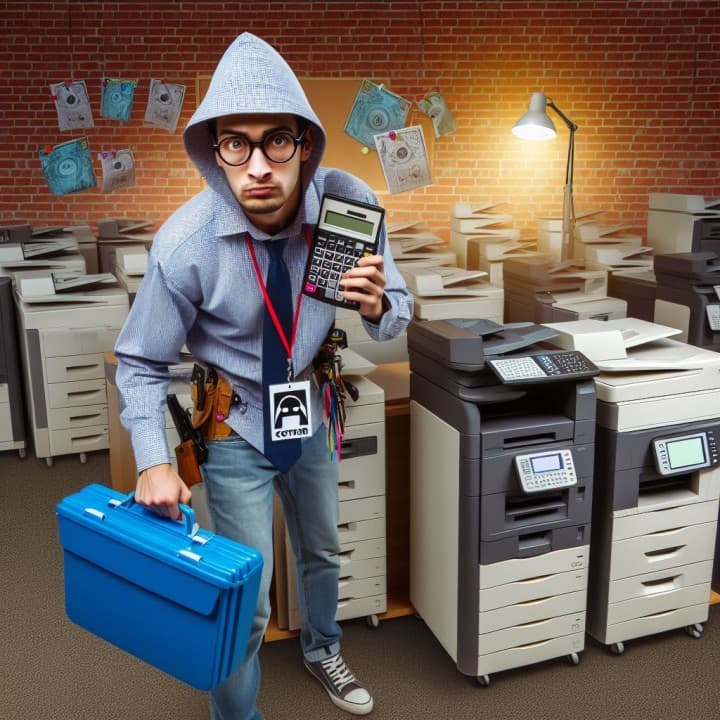
In the race to fortify their cybersecurity defenses, many businesses focus on deploying advanced firewalls and cutting-edge security solutions. However, a critical aspect often overlooked is the vulnerability posed by insecure protocols lurking within their networks. These protocols, such as HTTP, SMTP, Telnet, SMB, and PPTP, remain gateways for potential breaches and data compromises.
Despite investing in sophisticated firewalls, these insecure protocols tend to slip through undetected. Most firewalls are configured to passively allow these protocols, lacking the ability to actively analyze, interpret, or flag their usage. This default setting leaves businesses unaware of the insecure data transmissions occurring within their networks.
Fusion's Illuminate emerges as a beacon of light in this shadowy realm. This tool meticulously identifies and categorizes devices utilizing insecure protocols, revealing the transmission of sensitive information in plaintext. Implementing Illuminate within your network can be an eye-opener, exposing the stark reality of vulnerabilities lurking within your supposedly secure infrastructure.
For a quick and insightful assessment, Network Miner by Netresec provides a robust solution. This tool, when deployed on a laptop connected to a mirrored switch port, decrypts and displays all insecure data passing through the network. It vividly showcases documents, images, and even passwords transmitted in plaintext. An alarming revelation is often found in the unencrypted transmission of scanned confidential documents from multi-function printers—a potential disaster waiting to happen.
Businesses need to prioritize scrutinizing and securing their networks against these insecure protocols. Ignoring these vulnerabilities poses significant risks, potentially leading to data breaches, unauthorized access, and compromised sensitive information. Understanding and mitigating the risks posed by insecure protocols should be an integral part of any comprehensive cybersecurity strategy.
Ronald Bartels ensures that Internet inhabiting things are connected reliably online at Fusion Broadband South Africa - the leading specialized SD-WAN provider in South Africa. Learn more about the best SD-WAN in the world: 👉 Contact Fusion




